This policy verifies the generated JWS. If the signature value has been tampered or the signature is different, it will not allow the user to access the resource.
Configuration
The properties that have to be configured to use the policy are described below.
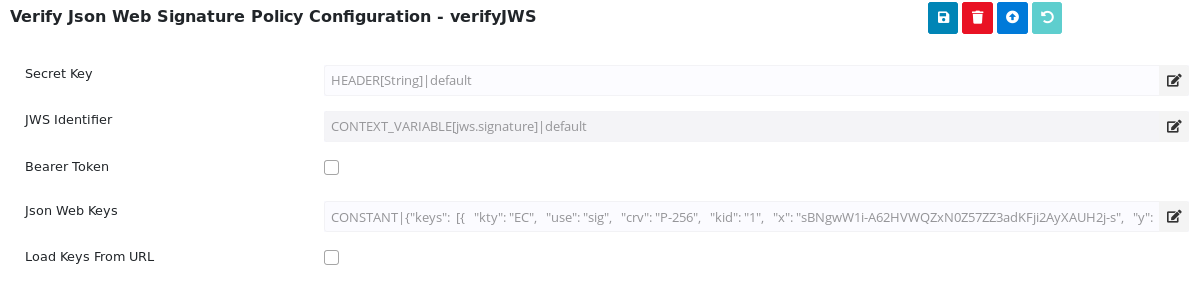
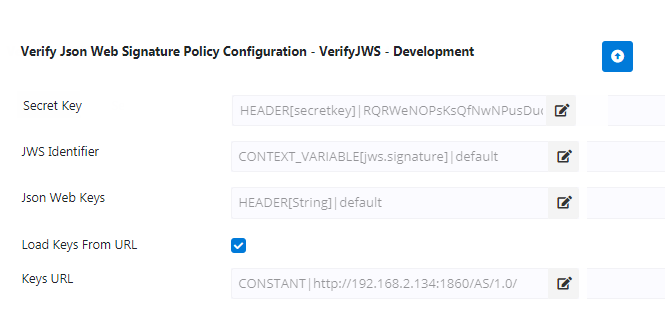
Figure 1: Verify Json Web Signature Policy configuration attributes
Property | Description |
JWS Identifier | Configure the Message Part Identifier with the source as header/Query parameter/context variable/constant through which the JWT is passed. |
Json Web Keys | Provide when an asymmetric algorithm like RS256 or ES256 is specified. |
Bearer Token | If the JWT to be verified is being sent in the request's "Authorization" Header as a bearer token, then enable this property. |
| Known Headers | Verify JWS policy examines "crit" parameter in the JWT header, if present, and checks that each value listed under "crit" contained in JWT provided for validation is present among the entries under this "Known Headers" element i.e the "Known Headers" must contain a superset of the items listed in JWT's "crit" header. Any header that is found in "crit" header that is not specified here among <KnownHeaders> causes the policy to fail. |
| Ignore Critical Headers | If this property is enabled, the policy ignores "crit" parameter in the JWT header. |
Secret Key | Provide when a symmetric algorithm like HS256 is specified. The minimum length of the string has to be 256, 384, 512 bits for HS256, HS384, HS512 respectively. |
Load Keys From URL | If Json Web Keys are exposed in a specific URL, then enable this property.
|
Keys URL | Specify the URL in which Json Web Keys are exposed. |
| Check JWKs Revocation Status | If this property is enabled, the public JSON Web Key being used for JWT verification shall be checked for its presence among the specified Revoked JWKs and verification would fail if the specific key is found to be revoked. |
| Revoked JWKs | Provide the revoked public Json Web Keys. |
| Load Revoked JWKs from URL | If Revoked Public Json Web Keys are exposed in a URL, then enable this property. |
| Revoked JWKs URL | Specify the URL in which Revoked Public Json Web Keys are exposed. If it's a secured URL, refer to |
Detached Content
In certain cases, it will be useful to protect the integrity of the content that is not itself contained in a JWS. Perform the following actions by detaching content as follows:
Create Assign Variable policy with the respective variable names and identifiers.
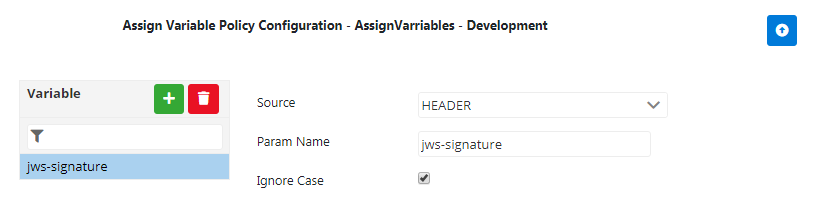
Figure 2: Verify Json Web Signature Policy configuration attributesGo to $FioranoHome/APIManagement\samples\JavaCallOuts\DetachedJWSClaim and run the compiled script. This creates a Classes directory containing a jar with compiled classes.
- Configure Java Call Out policy using the jar created above.
- Configure the Verify JWS policy as explained in this page.
Verifying a Json Web Signature
Request
Use browser/postman to send the request as below:
Response
Verifies the signature and allows to access the respective resources.