...
- Launch the Fiorano Studio for offline configuration of the FioranoMQ server.
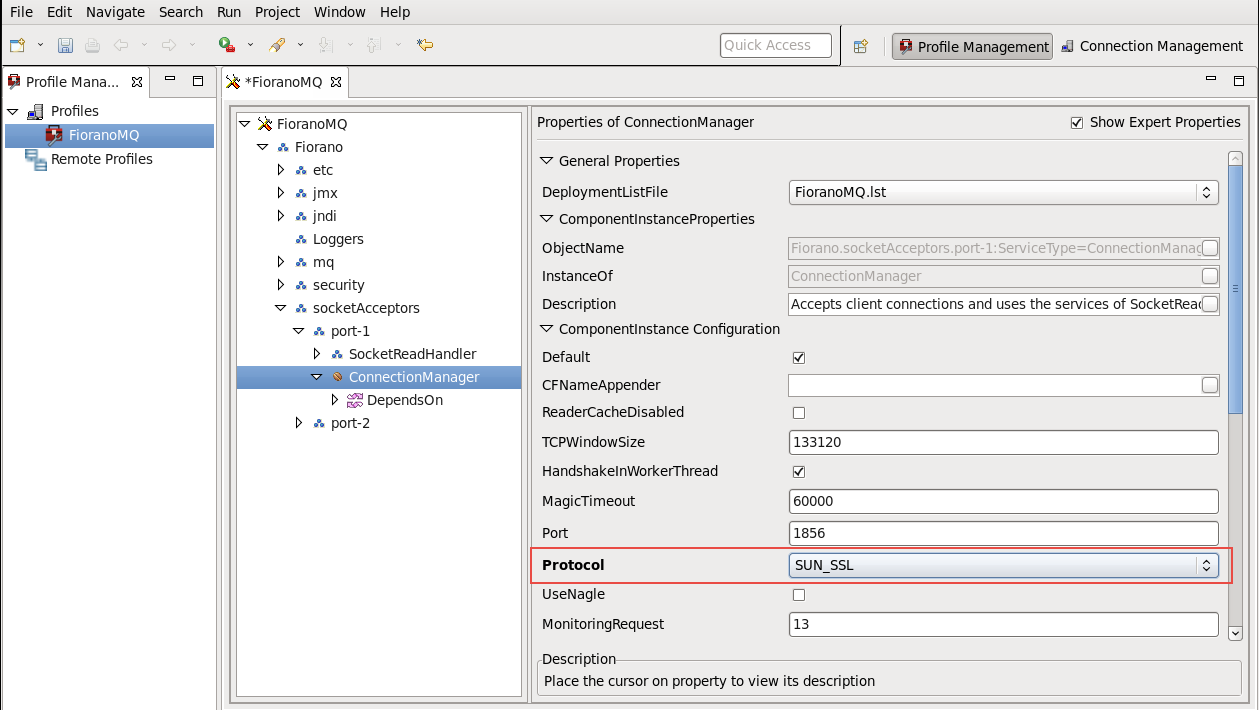
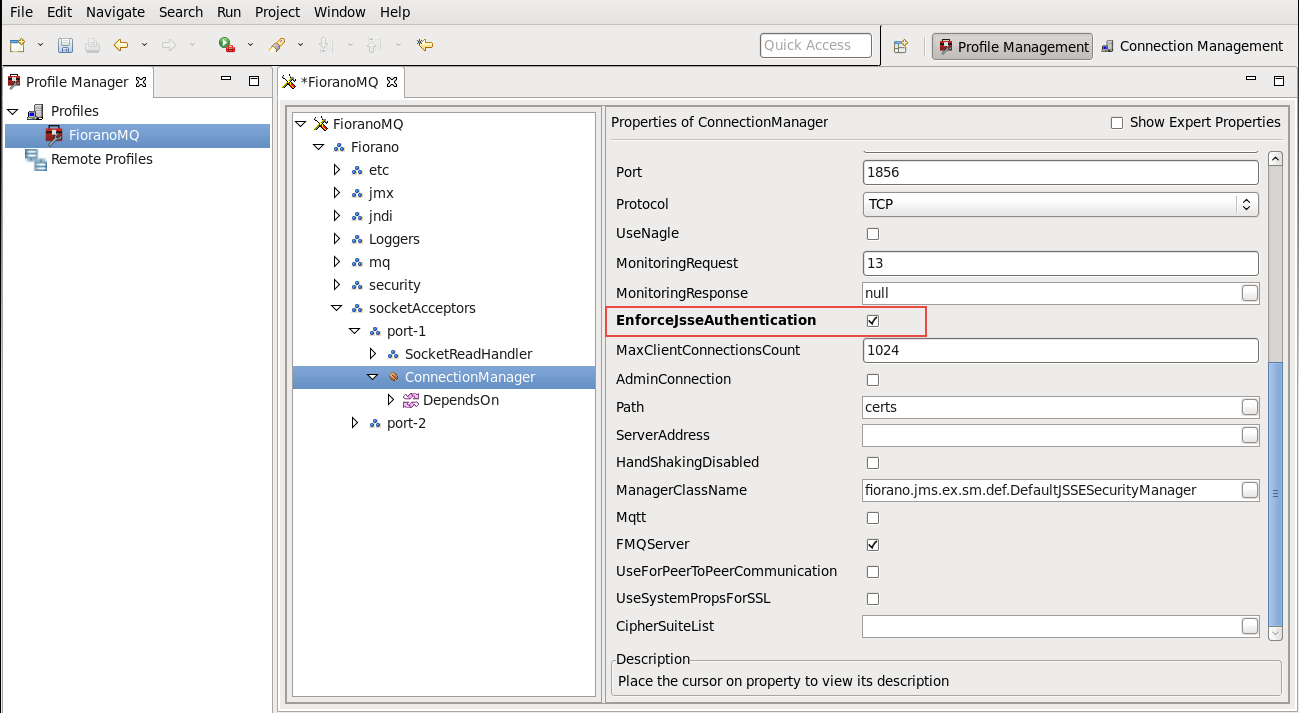
- Select Tools > ConfigureProfile from the menu bar, and open the profile needed. Navigate to %selectedProfile% > Fiorano > SocketAcceptors > Port-1 > ConnectionManager in the ServerExplorer.
- Change the Protocol property to SUN_SSL.
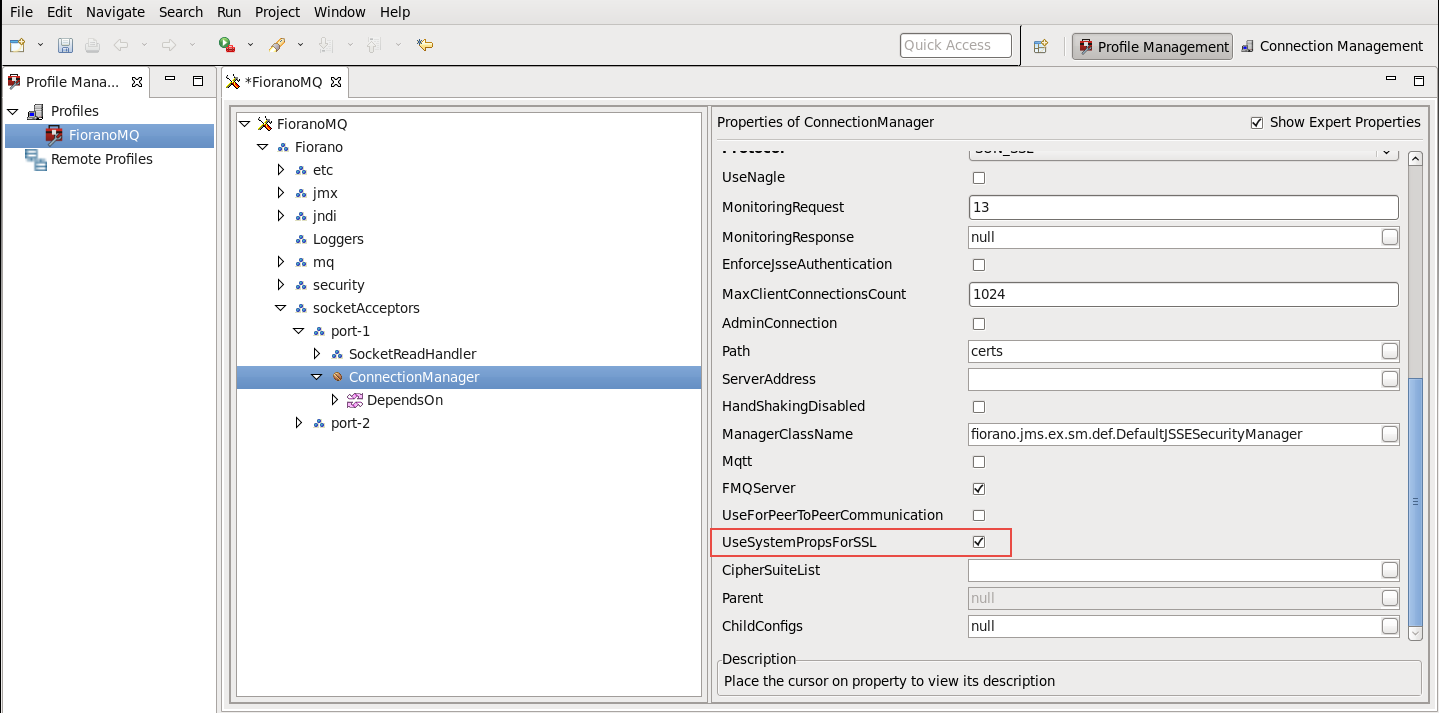
Change the UseSystemPropsForSSL to true (Optional)
Note The public/private keys and/or certificates used by the FioranoMQ Server can be loaded by specifying the related system properties, or by installing the appropriate security managers which can load the certificates. Please see the note at the start of Section 4.5.1.
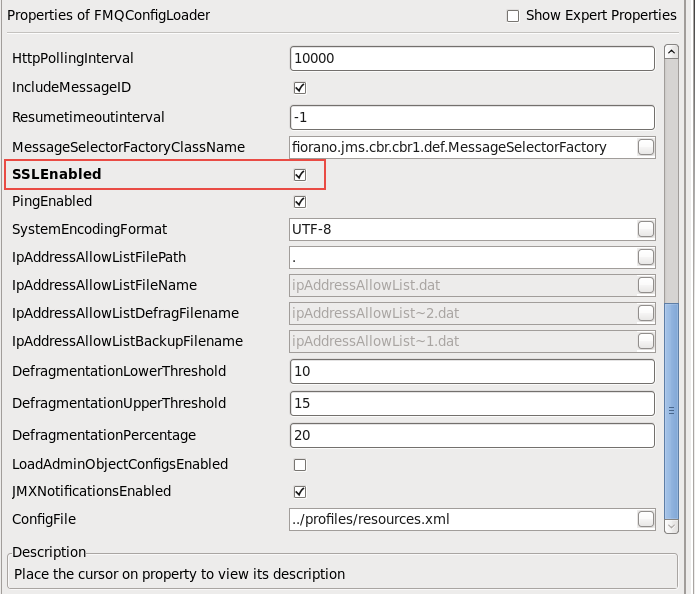
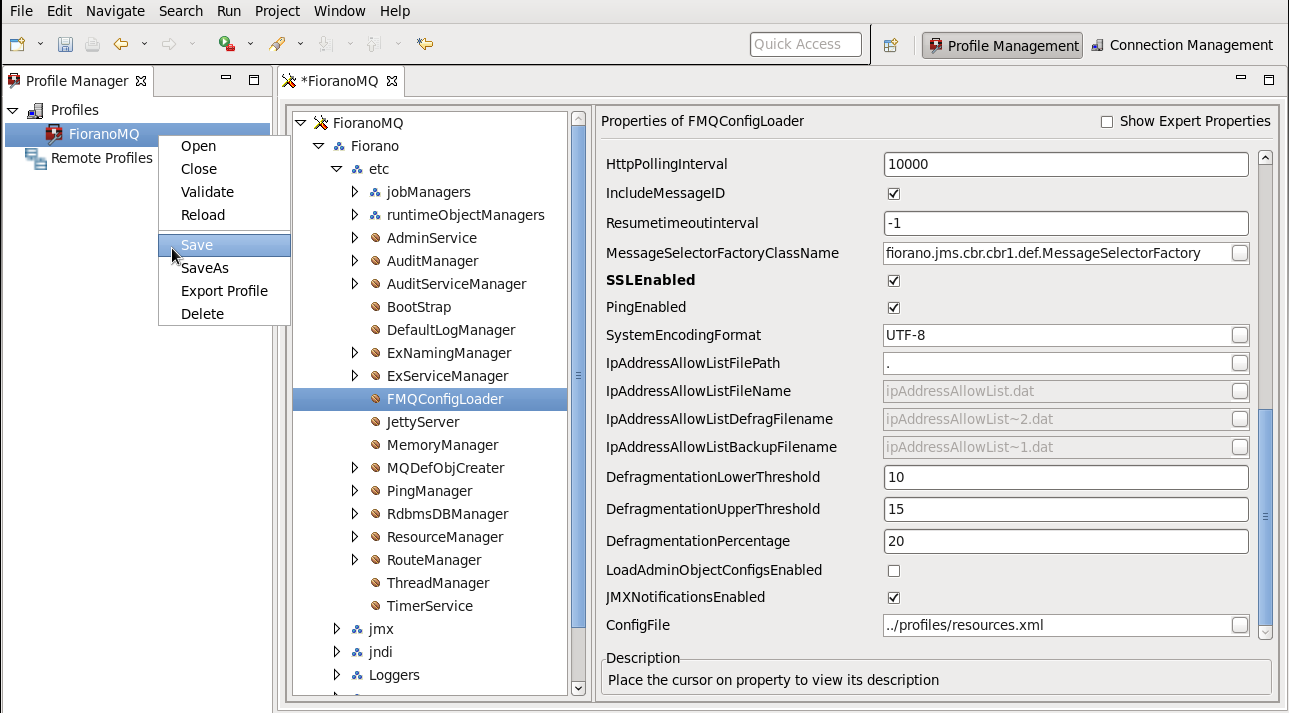
- Navigate to %selectedProfile% > Fiorano > etc > FMQConfigLoader. Right-click on FMQConfigLoader, and select Add Attribute from the pop-up menu. Add an additional attribute with the name SSLEnabled and with a value that is 'true'.

Navigate to %selectedProfile% > Fiorano > socketAcceptors > port-1 > ConnectionManager. Check the default value of property ManagerClassName. Ensure that the default value of ManagerClassName is fiorano.jms.ex.sm.def.DefaultJSSESecurityManager. (Optional)
Note This parameter is deprecated. Alternatively, in order to load the KeyStore and TrustStore, for initializing the context in which SSL Sockets are created, corresponding system properties should be set, and UseSystemPropsForSSL should be set to true.
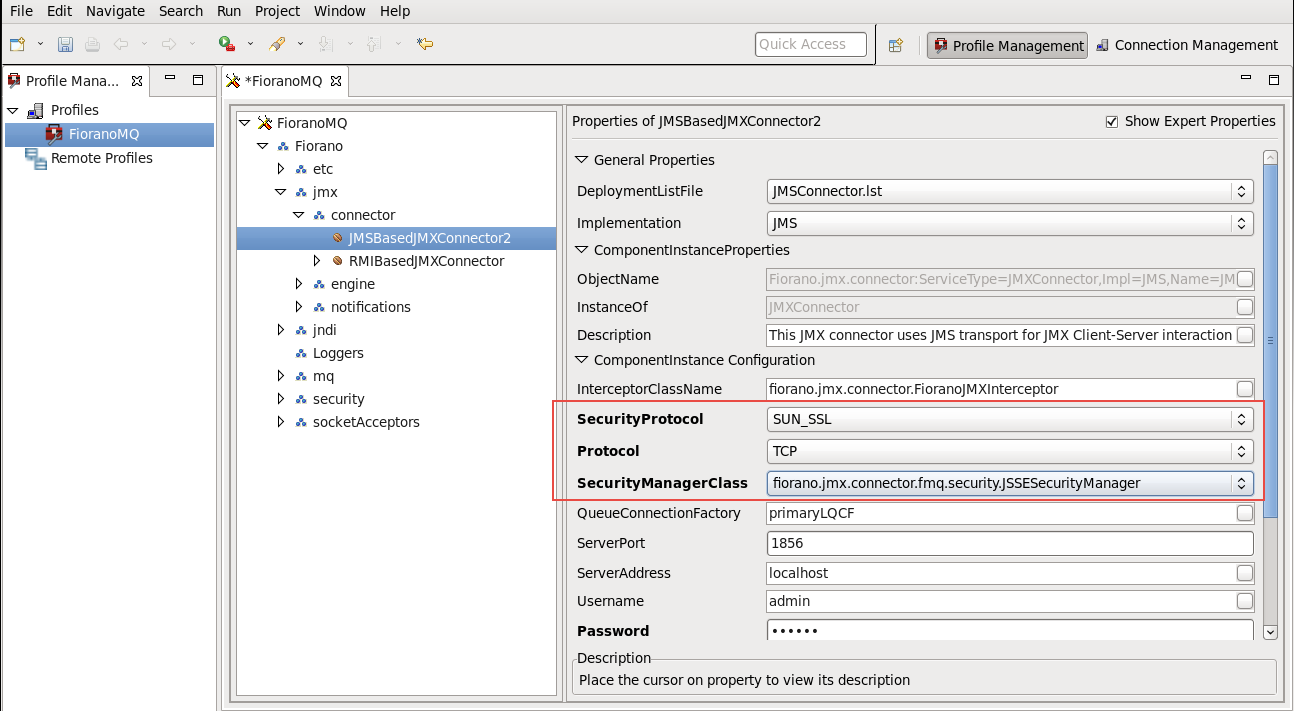
- Navigate to Fiorano > jmx > connector > JMSBasedJMXConnector2, and set the following properties to allow the JMSConnector to connect to the secure server.
- SecurityProtocol: SUN_SSL
- Protocol: TCP
- SecurityManagerClass: fiorano.jmx.connector.fmq.security.JSSESecurityManager
Right-click the FioranoMQ domain in the Profile Manager, and select the Save option from the pop-up menu.
areInfo Changes
theget saved in
filethe Configs.xml
file.

Clear the existing database using script ClearDB.bat located in %FIORANO_HOME%\fmq\bin directory.
Code Block ClearDB.bat %selectedProfile%
Start the Server again using script file fmq.bat located in %FIORANO_HOME%\fmq\bin directory.
Code Block fmq.bat –profile %selectedProfile%
The server starts accepting connections on TCP in the SSL (JSSE) mode.
...
EnforceClientAuthentication. (Refer to the profile screenshot below.) If the EnforceJSSEAuthentication parameter is enabled in ConnectionManagerConfigurations, then the server validates the certificates provided by the client.
To enable this, the keystore created should be added to the trusted Stores.
...
javax.net.ssl.trustStore=<path - is the path to the keystore>

4.5.4 Client Side Configuration
...