...
Encryp/Decrypt Configuration
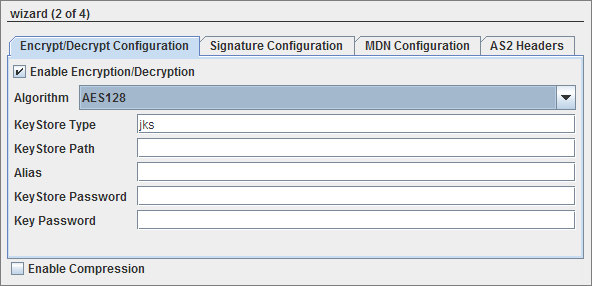
Figure 4: Encryption configuration details
...
- AES128
- AES192
- AES256
AES is a block cipher, 128, 192 and 256 being the variable key length in bits. - DESEDE3
DES, the Data Encryption Standard, is triple-DES encryption where an encrypt operation is encrypt-decrypt-encrypt, and decrypt is decrypt-encrypt-decrypt. - RC2
RC2 is a block cipher with a 64-bits block cipher with a variable key size that range from 8 to128 bits.
| KeyStore Settings | Description |
| KeyStore Type | For Java keystore file format, this property has the value jks(or JKS). You do not normally specify this property, because its default value is already jks. |
| KeyStore Path | Password to access the private key from the keystore file. |
| Alias | If the operation is SEND, Host private key alias should be configured.If the operation is RECEIVE, Partner public key certificate alias should be configured. |
| KeyStore Password | Password to unlock the keystore file (store password). |
| Key Password | Specifies the password for the key pair. |
...
Enable this to sign or verify signature of a message.
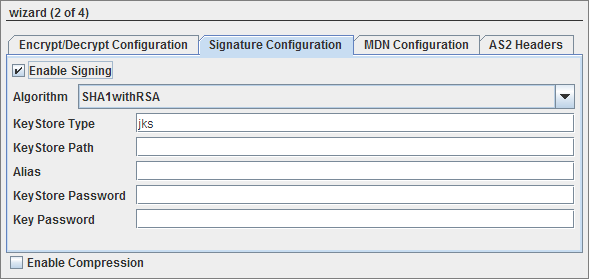
Figure 5: Signature configuration details
...
MDN provides a notification of disposition of a message, that is, whether it was decrypted and read by recipient, discarded before being read etc.
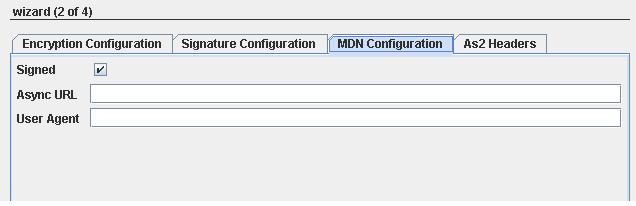
Figure 6: MDN configuration details
...
Enables compression of signature.
AS2 Headers
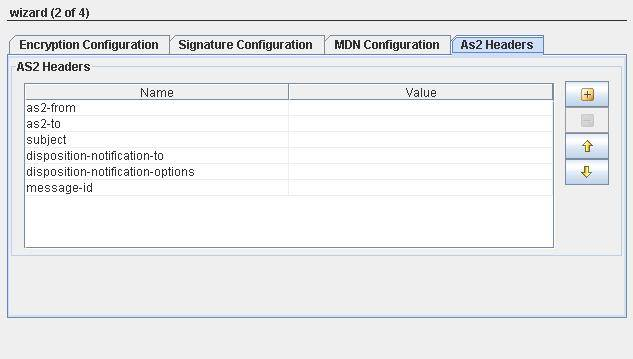
Figure 7: AS2 Headers details
...
- as2-from: Sender of AS2 message.
- as2-to: Receiver to whom the AS2 message is sent to.
- subject: Specifies the subject of the message.
- Disposition-notification-to: If this header present, it serves as a request for MDN to be returned. If it is accompanied by receipt-delivery-option header, then it is a request for an asynchronous MDN.If not, it is a request for Synchronous MDN. If this header property is absent, then MDN is not required.
- disposition-notification-options: MDN options that deals with signing like signed-receipt-protocol and signed-receipt-micalg.When signed-receipt-protocol is set to "pcks7-signature",is used to request a signed receipt from receiving party and indicates the format in which the signed receipt should be returned to requestor.Similarly, micalg specifies sender's desired algorithms with which receiver should sign MDN by.
- message-id: Identifier of message.
Keystore Configuration
Generating a Client Keystore
A keystore is a file that holds the public and private key pairs and certificates. The Keystore is a database of public and private keys. Java keytool is used to generate the public/private key pairs. Java keytool utility is present at %JAVA_HOME%/bin.
To generate a keystore, open the command prompt and type in the following command line and press the Enter key:
%JAVA_HOME%\bin\keytool -genkey -alias [alias name] -keystore [keystoreName] -keyalg [algorithm] -validity [days in integer] -storepass [store password] - keypass [key password]
Here is a brief description of the options used in the keytool command:
- -genkey: Requests keytool to generate a key pair
- -alias: Identifies the new key pair within the keystore
- -storetype: Declares the type of the keystore. JKS is the default type
- -keyalg: Declares the algorithm to be used; we're using the RSA public key algorithm, which is the default
- -storepass: Specifies the password for the entire keystore
- -keypass: Specifies the password for the new key pair
- -Validity: Validity of the key pair in days
- -keystore: File that holds the public and private key pairs
For example, you want to generate the keystore in the directory D:\WorkStudio\keystore, and then the command would look something like:
D:\WorkStudio\keystore>%JAVA_HOME%\bin\keytool -genkey -alias client1 -keystore client1.keystore -keyalg RSA -validity 365 -storepass cl1storepass -keypass cl1keypass
Press the Enter key. The result of the command is as shown in the Figure 1.

Figure 8: Running the keytool command
| Note |
|---|
You will have to type-in the answers to the questions that appear as shown above. The keystore file is generated in the specified directory. The next step is to create a truststore and add the server certificate in it. |
Refer to the SSL Configuration – Client perspective section to generate a Client Keystore, get the Digital Certificate of Partner and create the Client Truststore.
Host Alias
In the above samplereference section, "client1" is the host 's alias which must be provided while configuring AS2Connector as below:
- Send operation - value for Alias textbox in Signature Configuration panel.
- Receive operation - value for Alias textbox in Encrypt/Decrypt Configuration panel.
...
Partner
...
Digital certificate contains the public key and are stored in a Truststore(a keystore file). The Truststore is a file where certificates of trusted sites/parties can be retreived for authentication. To generate a truststore, you will have to first export and save the public key of the partner you are going to communicate. Sample is provided below to add certificate to the truststore:
...
| Note |
|---|
The process of copying and saving the digital certificate may differ from browser to browser. The concept is however the same. In the guide we have illustrated the process on Internet Explorer. |
Once you have saved the digital certificate, you are now ready to create the truststore.
Creating the Client Truststore
Perform the following procedure to create a trust store:
...
Partner Alias
...
Alias
In the above reference section, "mailserver" is partner's alias which must be provided while configuring AS2Connector as below:
...
| Anchor | ||||
|---|---|---|---|---|
|
The input schema is auto-generated for SEND mode based on whether Send connection details from input option is selected or not.
When it is selected, the input schema is generated as shown in figure and the sample input XML is are shown in figure 8 and figure 9.

Figure 148: Input Schema when Send connection details from the input option is selected
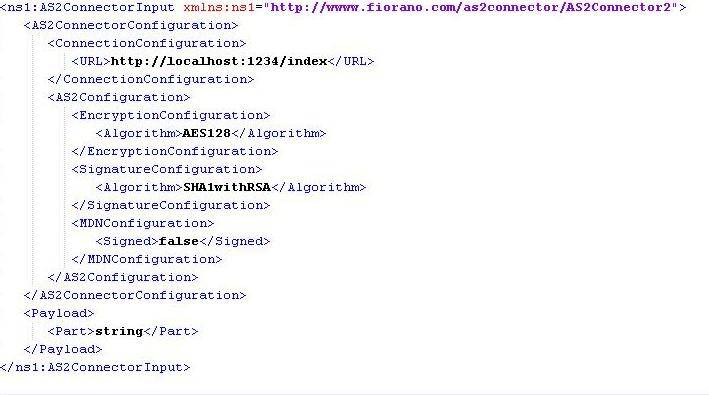
Figure 159: Sample Input XML when Send connection details from the input option is selected
When it is not selected, the input schema is generated as shown in figure and the sample input XML is shown in figure 10 and figure 11are shown in the figures below.
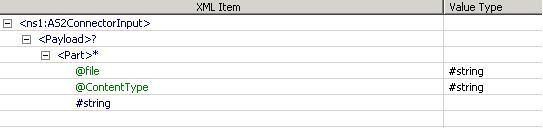
Figure 1610: Input Schema when Send connection details from input option is not selected
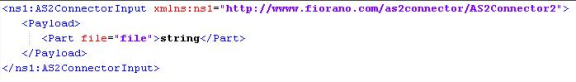
Figure 1711: Sample Input XML when Send connection details from the input option is not selected
For all other cases, no schema is set on input/output ports.
| Anchor | ||||
|---|---|---|---|---|
|
...
Scenario 1
Sending Encrypting AS2 message request Message and receiving AS2 message.
Configure one AS2connector in SEND mode and another in RECEIVE mode as described in Configuration section. Use a Feeder component to send the message part to AS2Connector configured in send mode and use a Display component to check the response.

Figure 18: Sample Event Process demonstrating SEND mode.
Connect a Display component to the output port of AS2Connector configured in RECEIVE mode and also the output port of Display to the response port of AS2Connector as shown in Figure 10.

Figure 19: Sample Event Process demonstrating RECEIVE mode
Scenario 2
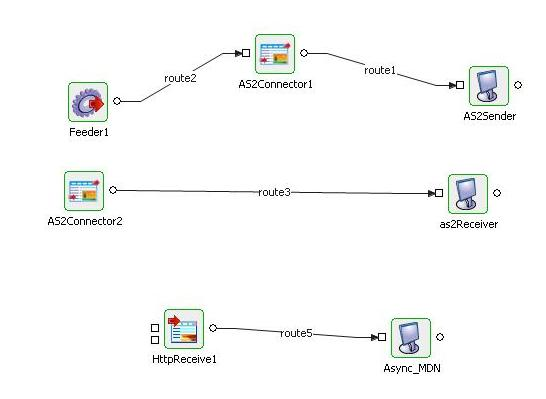
Figure 20MDN over different HTTP Connection (async MDN).
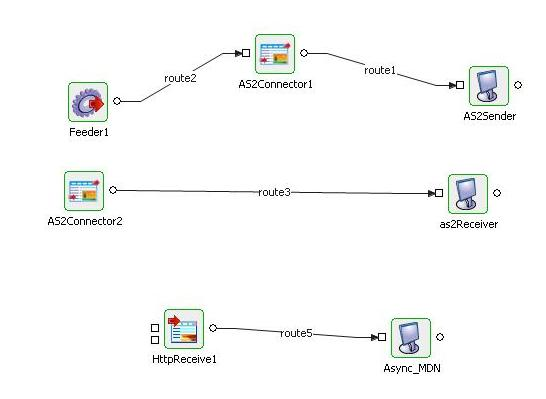
Figure 12: Sample Event Process demonstrating Scenario 2
Encrypting AS2 Message and receiving MDN over different HTTP Connection (async MDN).
Configure one AS2Connector in Send mode, provide encryption details and async URL. Configure another in Receive mode , give with decryption details.
Configure HTTPReceive to start on URL provided in async URL.
Sender Configuration
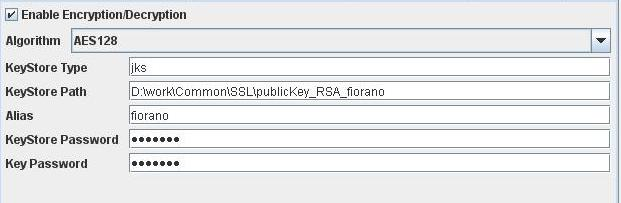
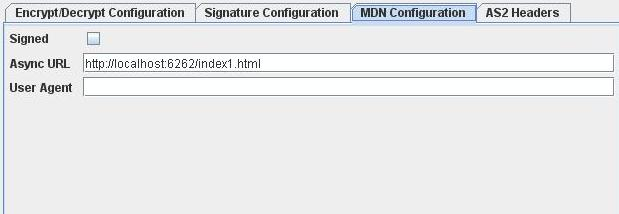
Figure 2113: Encryption and MDN Configuration in SEND mode.
Receiver Configuration
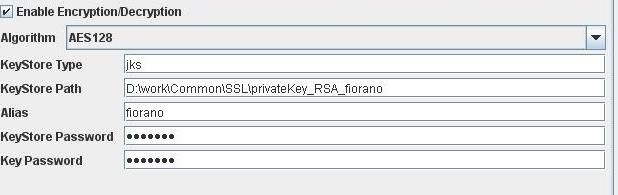
Figure 2214: Decryption Configuration in RECEIVE mode
Input
: Provide the same input as shown in Figure 11.
Output
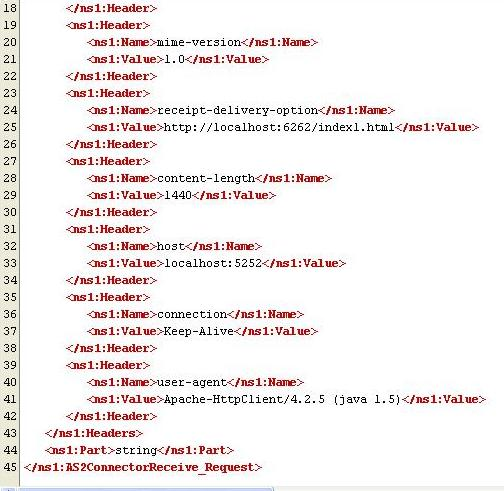
Figure 2315: Output Received on AS2Receiver(Display)
MDN Received on output at the output port of HTTPReceive :
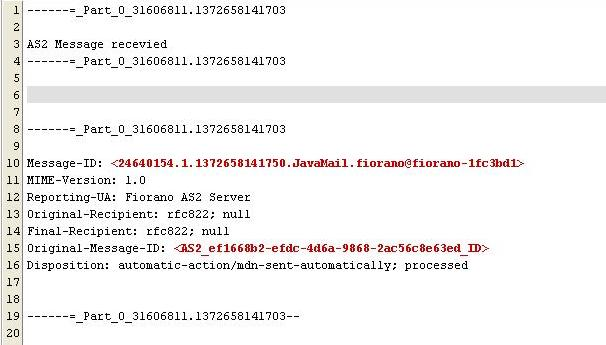
Figure 2416: MDN Received on Asyn_MDN(Display)