...
Drag the LDAPlookup adapter present in the Samples section of the Micro Service Palette. Double-click the component from Fiorano Orchestrator to launch the configuration wizard.
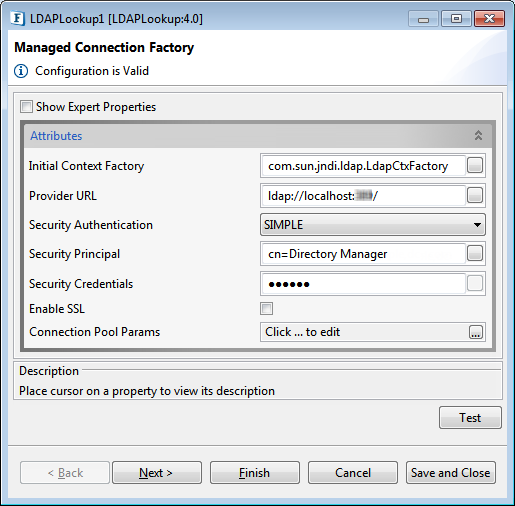
Figure 1 : Managed Connection Factory
Attributes
| Property | Description |
Initial Context Factory |
...
| Name of the initial context factory. | |
Provider URL |
...
| URL of the LDAP server. | |
Security Authentication |
...
| Specify the security level to use. | |
Security Principle |
...
Specify the identity of the principal for authenticating the caller of the service. |
...
|
...
| |
Security Credentials |
...
| Specifies the credentials of the principal for authenticating the caller of the service. | |
Enable SSL |
...
| Specify if SSL is to be used during connection. | |
SSL support Mode | Specify whether to enable SSL via SSL Ports or bu using Start TLS extension in LDAP. |
Trust Store Location | Location of the Trust Store |
Trust Store Type | Provide type of the Trust Store; default value is "jks". |
Connection Pool Params |
...
Various parameters to be used in connection pooling of EIS connection. Refer to the Connection Pool Params section in the Common Configurations page. |
Interaction Configurations

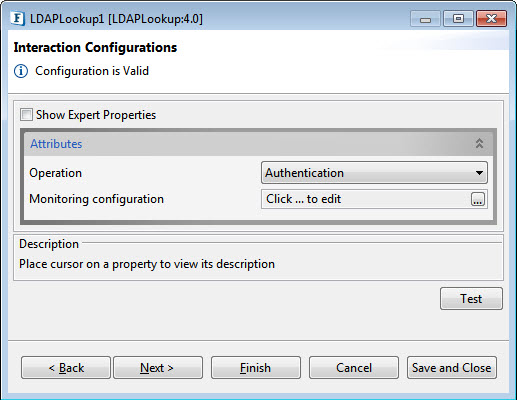
Figure 2: Interaction Configurations
...
- Authentication
- Lookup
- Compare
- Bind
- Modify
- Delete
- Rename
- Change Password.
...
- Poll
There areseparate attributes for different Operation options; each one is described below disabling Expert Properties as it appears the same for all options.
Authentication
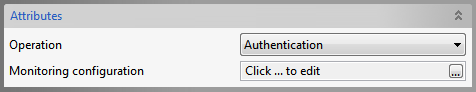
Figure 3: Authentication Operation Attributes
The component acts as an authenticator. The properties configured in the Managed Connection Factory panel are the ones required for authentication.
Lookup
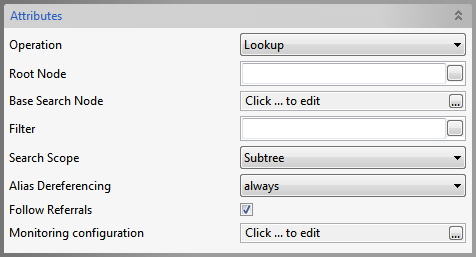
Figure 4: Lookup Operation Attributes
| Property | Description |
Root Node |
...
| Specify |
...
| the Distinguished Name (DN) |
...
| of an entry, the sub-tree of which you want to view in the editor that opens with the property. |
Base Search Node |
...
| Choose the DN of the entry whose sub-tree and the entry by itself have to be searched for |
...
Filter |
...
| Specify the search constraints to be applied on the entry represented by 'Base Search Node' and the entries in its sub-tree. | |
Search Scope |
...
| Specify the scope of the search. | |
Alias Dereferencing |
...
| Specify how aliases are to be dereferencing |
...
| during search |
...
| operation. |
Follow referrals |
...
| Specify whether referrals are to be followed or ignored. |
...
Compare
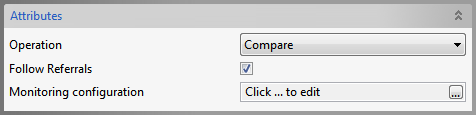
Figure 5: Compare Operation Attributes
Follow Referrals
:Specifies whether referrals are to be followed or ignored.
Bind
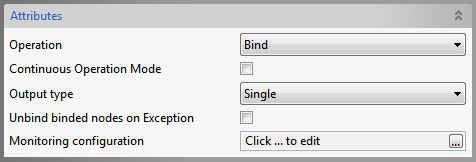
Figure 6: Bind Operation Attributes
Continuous Operation Mode
:If true, operations on the subsequent nodes are continued if an exception occurs while processing some node, in case of processing multiple nodes in a single input. If false, operation is stopped if any exception occurs.
Output Type
: Single- A single output for success of operations on all nodes. Multiple-Multiple outputs.
Unbind binded nodes on Exception
:Specifies the action(Unbind already binded nodes/Leave them binded) when an exception occurs while adding some node.
Modify
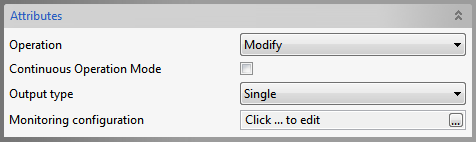
Figure 7: Modify Operation Attributes
Continuous Operation Mode and Output Type
: Refer the Bind section above.
Delete
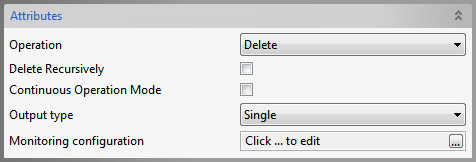
Figure 8: Delete Operation Attributes
Delete Recursively
: Specifies whether a recursive delete must be done. If true, and if the DN specified isn't a leaf, its children and all their children are deleted are down the tree. If false, only the leaf entries are deleted
Continuous Operation
...
Mode and Output Type
: Refer the Bind section above.
Rename
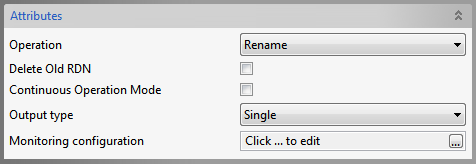
Figure 9: Delete Operation Attributes
Delete old RDN
:Delete previous Relative Distinguished Name
Continuous Operation
...
Mode and Output Type
: Refer the Bind section above.
Change Password
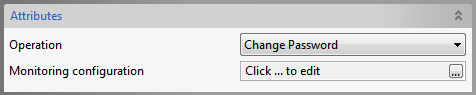
Figure 10: Change Password Operation Attributes
The properties configured in the Managed Connection Factory panel are the ones required for Change Password operation.
...
Poll
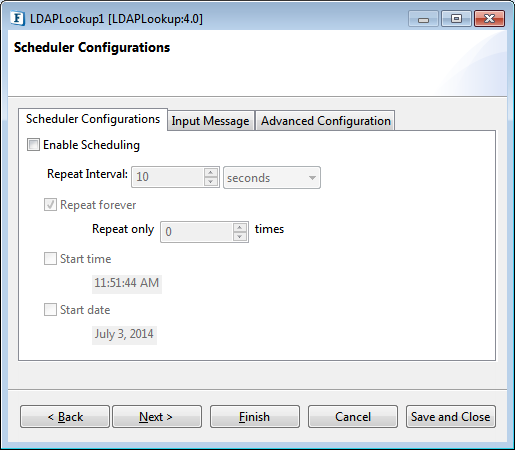
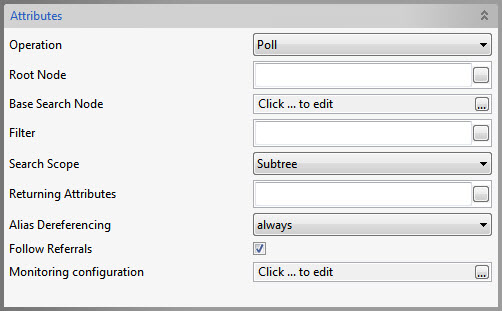
Figure 11: Poll Operation Attributes
Returning Attributes
Specify the list of attributes to be returned when a change occurs.
| Info | ||||
|---|---|---|---|---|
| ||||
mail,cn |
| Tip |
|---|
For all other attributes like Root Node, Filter etc., refer to the Lookup section above. |
Monitoring Configuration
Refer to the Monitoring Configuration section in the Common Confirmation.
Expert Properties
Enable the Expert Properties view to configure these properties.
| Warning |
|---|
Expert properties are meant for advanced users. |
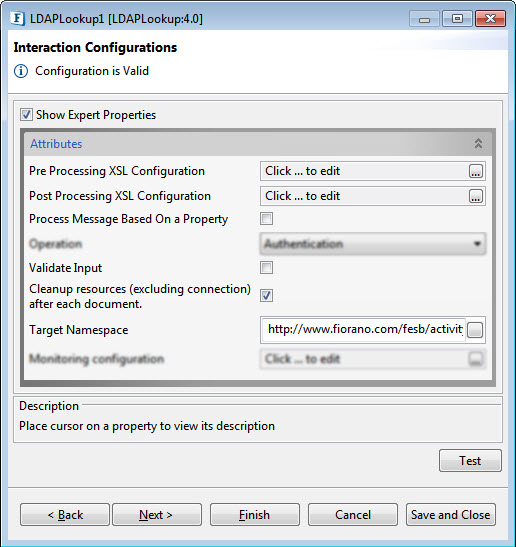
Figure 12: KafkaConnector CPS with the Expert Properties enabled and highlighted
Pre Processing XSL Configuration
Pre Processing XSL configuration can be used to transform request message before processing it. Click the ellipses button against the property to configure the properties.
Refer to the Pre/Post Processing XSL Configuration section under the Common Configurations page for details regarding Pre Processing XSL configuration and Post Processing XSL configuration (below).
Post Processing XSL Configuration
Post Processing XSL configuration can be used to transform the response message before sending it to the output port.
Process Message Based on Property
The property helps components to skip certain messages from processing.
Refer to the Process Message Based On a Property section under the Common Configurations page.
Validate Input
If enabled, LDAPLookup validates the input received.
| Note |
|---|
If the Input validation is disabled, it does not validate the input and thereby increases the performance. However, it may cause undesired results if the input XML is not valid. |
Cleanup resources (excluding connection) after each document
This closes all the resources except for the connection after every request. If the less processing time is more important than the less memory usage, then it is recommended to disable this property and vice versa.
For more details, refer to the respective section under in the Common Configurations page.
Target Namespace
Target Namespace for the request and response XML messages.
For more details, refer to the respective section under in the Common Configurations page.
Scheduler Configurations
On enabling scheduling, we can set the repeat interval in milliseconds/seconds/hours/minutes/days unit and the repeat period can be set as Repeat forever or the number times can be specified too as an alternative.
Another scheduling option is to set the start time and date which helps to control the start of of scheduling process process.
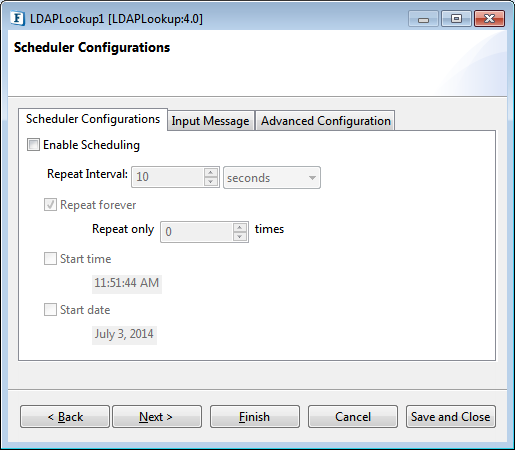
Figure 13: Scheduler Configurations
Please refer Scheduler Configurations section in the Common Configurations page.
Error Handling Configuration
...
Transport Configurations
Transport Configurations panel is used to configure messaging properties when the component is configured in Scheduling mode.
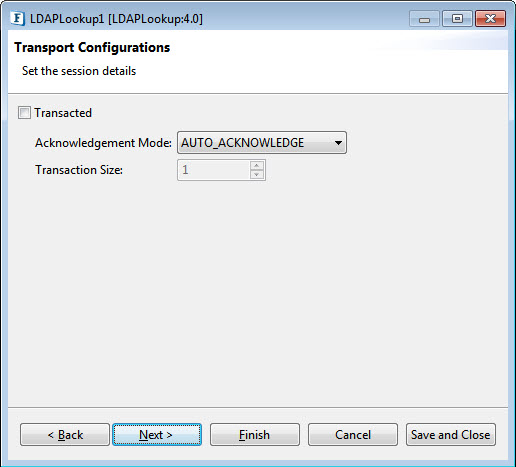
Figure 14: Transport Configurations
Please refer to the Transport Configurations section in the Common Configurations page.
Error Handling Configuration
The remedial actions to be taken when a particular error occurs can be configured here. Click on the ellipsis button against this property to configure Error Handling properties for different types of Errors. By default, the options Log to Error Logs and Send to error port are enabled
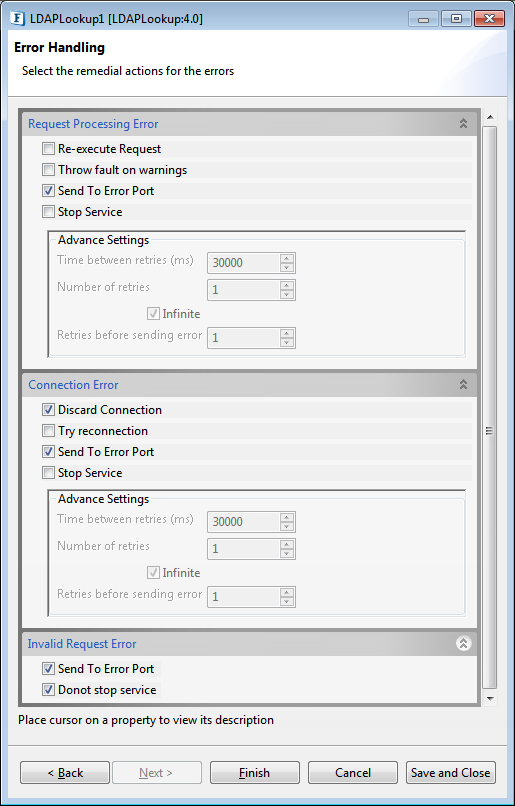
Figure 15: Error Handling Configurations
| Tip |
|---|
Refer Refer to Error Handling section in Common Configurations for more information. |
...
Sample 1: Bind Configuration
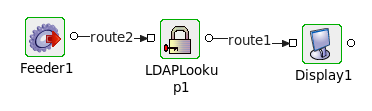
Figure 1316: LDAPlookup event flow
- Connect the LDAPLookup1 adapter to a Feeder and a Display as shown in the figure above.
- Launch the configuration wizard by double-clicking the LDAPlookup icon in the Fiorano Orchestrator.
- Set the fields in the Managed Connection Factory configuration page as shown in Figure 1.
- Choose the Operation as 'Bind' in Interaction Configuration panel.
- Save and close the wizard and open feeder CPS.
To create a user in the server, enter the following in the feeder :
Code Block language xml <?xml version="1.0" encoding="UTF-8"?> <ns1:Input xmlns:ns1="http://www.fiorano.com/fesb/activity/LDAPLookup1/In"> <Node> <dn>cn=testuser,dc=fiorano,dc=com</dn> <objectClass>person</objectClass> <cn>testname</cn> <sn>surnam</sn> <userPassword>fiorano</userPassword> <Description>Description</Description> <AdditionalAttribute> <Name>location</Name> <Value>hyd</Value> </AdditionalAttribute> </Node> </ns1:Input>Note The value of "dn" will depend on server type. The above is for 389-ds server.
- Perform CRC (resource and connectivity) and then launch the event process. This will create a new user in the 389-ds server.
...
- Follow steps 1-3 from sample 1.
- Choose the Operation as 'Authentication' in Interaction Configuration panel.
- Click the Test button.
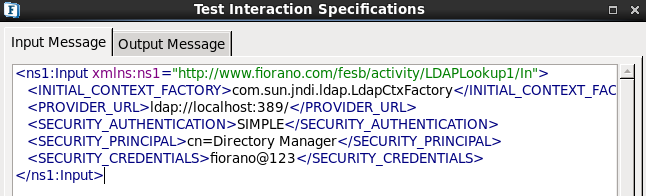
Figure 1417: Authentication Configuration - Enter the above details in the Input Message tab.
- Click the Validate button and then click the Execute button to get the following result.
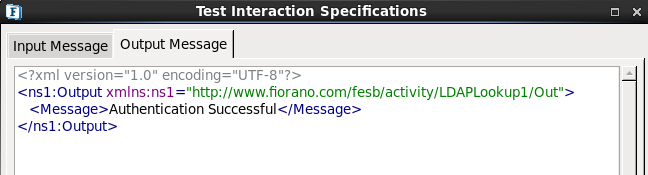
Figure 1518: Authentication Configuration Result
...
- Follow steps 1-3 from Sample 1.
- Choose the Operation as 'Change Password' in Interaction Configuration panel.
- Click the Test button.
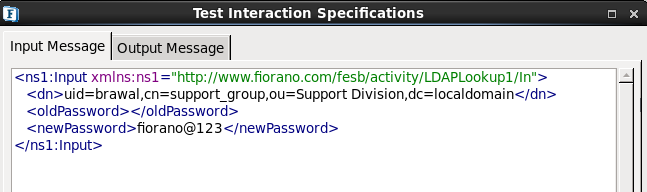
Figure 1619: Password Change Configuration
- Specify the Distinguished Name, old password and new password
- Click Validate then click Execute to get the following result.
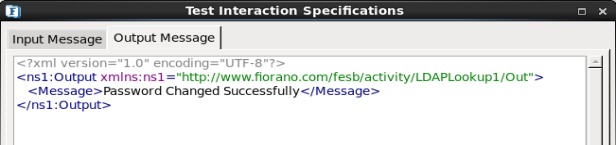
Figure 1720: Password Change Configuration – Result
...
- Follow steps 1-3 from Sample 1.
- Choose the Operation as 'Delete' in Interaction Configuration panel.
- Click the Test button.
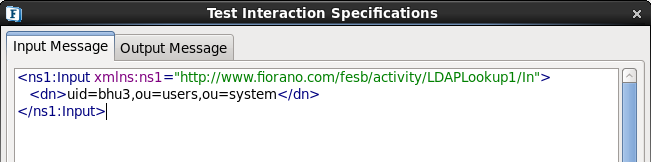
Figure 1821: Delete Configuration specify-dn
- Specify the distinguished name of the entry to delete.
- Click Validate and then click Execute to get the following output.
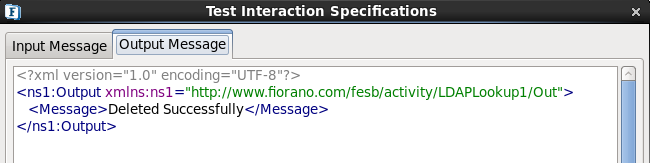
Figure 1922: Delete Configuration - Result
...
- Follow steps 1-3 from Sample 1.
- Choose the Operation as 'Rename' in Interaction Configuration panel.
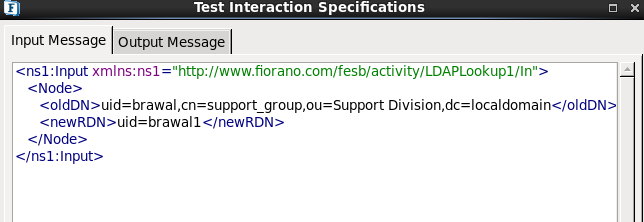
Figure 2023: Rename Configuration
- Enter the old Distinguished Name and the new relative distinguished name.
- Click Validate and click Execute to get the following result.
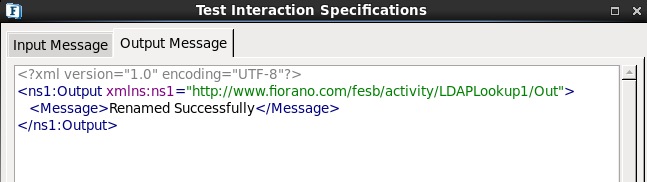
Figure 2124: Rename Configuration - Result
...